BACKGROUND
Despite constant technological development in informatisation and the introduction of restrictive legal regulations, breaches of sensitive personal data are increasing in frequency (Schatz & Bashroush, 2019). The law of protection of personal data serves to implement in practice the regulation of the European Parliament and of the Council on the protection of natural persons concerning the processing of personal data and on the free movement of such data. The specific provisions for the healthcare sector concern the doctor- and nurse-patient confidentiality as well as the confidentiality binding healthcare administration employees. They comprise administrative, civil, criminal, and labour law (Jackowski, 2018). In the USA alone, the costs of personal data breaches in the healthcare sector are estimated to be 7 billion dollars annually (Fernández-Alemán et al., 2015). However, breaches might be under-reported due to undetected instances or, conversely, the desire to conceal them out of fear of losing reputation and clients. The media report spectacular cases of unlawful access by hackers to clients’ medical information. The analysis of articles on medical informatics shows that the topic of information security (IS) does not receive much attention (Gülkesen & Haux, 2019). However, almost 60% of all personal medical data security breaches result from employee carelessness or neglect, or not following appropriate IS guidelines and procedures (Verizon Risk Team, 2018). In turn, these result from a lack of IS culture, attitudes, and concrete behaviours (Simmonds, 2018). Cybersecurity practices in healthcare are at a much lower level than in other areas of business, for example, finance (Apkan, 2016). Preventing data breaches involves changing the behaviours and attitudes of healthcare employees and cooperating entities (Bulgurcu et al., 2009). Increasing digitisation of healthcare delivery is causing researchers and information technology specialists to highlight the growing need for effective information management to ensure safe and high-quality care (Thye et al., 2020).
The healthcare sector is the only one in which more internal than external entities are responsible for sensitive personal data breaches. “Ransomware” attacks are becoming a problem, constituting over 80% of malware cases in healthcare. A low risk of perpetrator detection, the ease of carrying out such an attack, low levels of security and procedure adherence, and a possibility of obtaining a high ransom lead to healthcare institutions being especially vulnerable to such attacks, resulting in the loss of control over patient and personnel personal data. Additionally, the high costs of potential damages payments and the loss of reputation make healthcare firms more likely to pay such ransoms. Medical data are especially sensitive due to their value. Illegally obtained data of this nature might be wrongfully used by unauthorized entities (Bulgurcu et al., 2009). It is important that hospital information systems are designed to avoid unauthorized access to information (Coppock et al., 2017).
The greatest amount of medical data is lost through electronic channels (hacking) and theft of equipment such as laptops or tablets containing unsecured medical or personal data (Anderson et al., 2017; McCoy & Perlis, 2018). Loss of data is also caused by not following appropriate security procedures, disclosures to unlawful persons, and careless employee behaviour (Liu et al., 2015). Due to the potential for leakage of such information, patients may be concerned about providing complete information to healthcare professionals about their mental or sexual health (Peikari et al., 2018). Patients must provide all crucial information for appropriate diagnosis and treatment to healthcare service providers. The patients’ concerns about unlawful disclosures and improper use of sensitive medical data might lead them to refuse to provide such critical information during treatment. As a result, these concerns and the withholding of vital information might expose the patients to medical risk and harm their health. Telecommunications technology can be a way to overcome social phobias, but it should not generate additional IS concerns (Fardoun et al., 2020). Despite the possibility of the loss of sensitive data, telecommunications technology and telemedicine are becoming increasingly common and improve the quality of medical service provision (Grover et al., 2020; Kopanitsa, 2017). For example, the National Health Service has published competencies required of nurses for information technology (IT), which include necessary IT skills, clinical informatics, information governance, and IS (Pulverman & Meston, 2020). Even though more than ten years have passed since their publication, the competencies remain relevant.
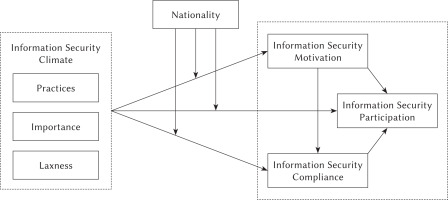
Basing on the results of studies and analyses of IS in the healthcare sector, we focused on employee attitudes and behaviours, analysing them in the context of organizational climate, commonly equated with organizational culture. Organizational climate can be defined narrowly as “the shared perception of the way things are around here” or, more broadly, as “the shared perceptions of and the meaning attached to the policies, practices, and procedures employees experience and the behaviours they observe getting rewarded and that are supported and expected” (Bond, 2007; Reichers & Schneider, 1990; Schneider et al., 2013). Such an understanding of organizational climate has been successfully used to change employee attitudes and behaviours. Examples include safety climate, diversity climate, overwork climate, violence prevention climate, and service climate (Greenslade & Jimmieson, 2011; Hallett et al., 2018; Madera et al., 2016; Olds et al., 2017; Piotrowski & Jurek, 2019). A characteristic feature of these areas is that appropriate guidelines, procedures, training, and assessments are not sufficient on their own for implementing lasting changes in employee behaviour. Using the organizational climate approach allows key areas to be identified and desired changes to be pinpointed. Information security climate refers to the common and recognised practices in the workplace defining how IS is treated in the organization (Lowry & Moody, 2013). Kessler et al. (2019) designed a 9-item IS climate scale that assesses how employees view the policies and practices concerning safe data handling. It contains three subscales: (a) practices, that is, behaviours and discussions that are actively initiated by the supervisor to promote information security; (b) importance placed on the protection of confidential data; and (c) laxness, that is, prioritizing other work activities over IS. Alnatheer’s (2014) research showed that IS culture is affected by organizational culture and, in turn, national culture affects organizational culture. Ameen et al. (2021) found that nationality can influence IS compliance. Therefore, we considered nationality as a moderating variable in the conceptual model used in our study. The results obtained by Vance et al. (2012) showed that IS motivation has an important role in IS compliance. Using the theory of planned behaviour, we deduced that IS compliance can improve IS participation by modifying behaviour (Karjalainen et al., 2020).
The conceptual model used in this study is shown in Figure 1. It proposes interrelationships among IS climate, its dimensions, and dependent variables.
PARTICIPANTS AND PROCEDURE
PARTICIPANTS
Three hundred and thirty-one nurses participated in the study. Thirty-one of them were male, aged M = 42.74, SD = 9.62; min. = 22 years, max. = 67 years. Sixteen per cent had a secondary education, 42% had a Bachelor’s degree (all of the 199 Iranian nurses and 117 Polish nurses), and 42% had a Master’s degree.
MEASURES
A structured questionnaire was used for data collection. The IS Climate Index was obtained upon request and with consent from Kessler et al. (2019) and was translated into Polish and Persian. A psychologist with a background in English philology carried out the Polish translation. Then, a second person with the same qualifications back-translated the questionnaire into English. Two experts then prepared the final version of the Polish and Persian translations. In the current study, Cronbach’s α for the total scale was .89. Cronbach’s α values for other variables are shown in Table 1.
ETHICS
Participation in the study was voluntary and anonymous. Respondents gave informed consent to participate. The study was conducted in accordance with the Helsinki Declaration. The study was approved by the NHS Health Research Authority South East Coast – Surrey Research Ethics Committee (REC reference: 14/LO/1977) and all participants were informed that they were free to refuse to participate or withdraw from the study at any time.
DATA ANALYSIS
Descriptive statistics and correlations between the individual questionnaire items (Pearson’s r) were analysed first. Next, a confirmatory factor analysis (CFA) was carried out using SPSS version 22 and SmartPLS 3. SmartPLS 3 has several advantages for researchers for principal component analysis rather than confirming a theoretical model (Chin et al., 2003). Also, it allows the analysis of results of structural models and measurements with less restriction on sample size (Vinzi et al., 2010).
Cross-loadings of the CFA, average variance extracted (AVE), and latent correlation analysis were used for measuring discriminant validity and model tests. For all exogenous and endogenous constructs used, the statistical results exhibited common method bias (Chin, 2010). Finally, the coefficient of determination and the statistically significant values of the path coefficients were used to estimate the structural model (Podsakoff et al., 2003).
RESULTS
MEASUREMENT MODEL
We conducted a CFA to test the measurement model. A latent correlation analysis was performed to test construct validity. The square root of the AVE for each construct assessed the convergent validity for all latent variables, compared to intercorrelated values across other constructs. The analysis showed that the AVEs are greater than the intercorrelations of other latent variables, which indicated that each respective construct is distinct from the other constructs in the measurement model. The square root of the AVE was also over 0.70, implying that each latent construct explained the indicators to a greater extent than error variance. Thus, these results confirmed both discriminant and convergent validity. The internal consistency calculated by composite reliability was also tolerable (over 0.70; see Table 1).
STRUCTURAL MODEL ESTIMATION
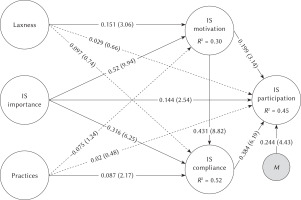
A partial least squares (PLS) structural model with bootstrap resampling using SmartPLS 3 was employed to test the relationships in the proposed model and calculate the t values. Model fit for combined Iranian and Polish data was as follows: SRMR = 0.068, d-ULS = 0.799, d-G = 0.229, χ2 = 414.63 and NFI = 0.848. These values indicate a good model fit. As shown in Figure 2, 45% of IS participation was predicted by other variables, and IS compliance moderated the effect of IS motivation and IS participation (β = .24 vs. β = .20).
A series of regression analyses were conducted to test the validity of the results obtained from the PLS method. β (path coefficient) and t values for each variable in the Iranian and Polish data are shown in Table 2.
Table 2
Robustness test
A multi-group analysis was used to analyse the effect of nationality. It showed that nationality had a significant effect on the relationship between IS motivation and IS compliance, IS compliance and IS participation, and IS importance and IS compliance (see Table 3).
Table 3
PLS multi-group analysis for the effect of nationality on the relationships between variables in the Iranian and Polish samples
DISCUSSION
The current study aimed to investigate the factors affecting IS participation in a sample of Iranian and Polish nurses. Information security laxness had a significant effect on IS motivation. This variable explained almost 30% of IS motivation. Information security motivation plays an important role in IS implementation (Urbach & Ahlemann, 2010). Motivation influences all areas of human behaviours (Guhr et al., 2019). Nurses’ perception of the importance of IS had the greatest effect on IS motivation. Only this variable had a significant effect on IS compliance and participation. Thus, perception of IS importance is one of the most important variables for organizations because when individuals choose to disregard IS policies and procedures, all of the others managers’ solutions will fail (Apkan, 2016; Toode et al., 2011; Vance et al., 2012).
The theory of planned behaviour also confirms this relationship, showing that individual perception of IS importance influences IS compliance (Apkan, 2016).
The current results show that nurses’ IS compliance has a direct effect on IS participation and can also moderate the effect of IS motivation on IS participation. Lee et al. (2016) argue that if nurses comply with IS, the stress related to the need to employ IS policies in practice can decrease (Kirsch & Boss, 2007). Reducing workload and emotional demands increases work engagement (Huang et al., 2011). This can manifest itself in many dimensions of medical personnel’s work. Reducing nurses’ stress stemming from IS practices and policies can improve IS participation and can constitute an organizational opportunity to implement IS strategies in hospitals.
Fifty-one per cent of nurses’ results on IS compliance can be explained by the perception of IS importance, practices, and IS motivation. This result was confirmed by Humaidi and Balakrishnan (2015). They stated that organization managers can adopt an appropriate leadership style to improve employee motivation and, in turn, their IS compliance. Bulgurcu et al. (2009) argued that rules, standards, and practices regarding IS in the organization would increase employee IS compliance.
In Iran, nurses’ IS climate is lower than in Poland (3.05 vs. 3.99), and this difference is statistically significant. This result can be interpreted with reference to the Human Development Index for countries (Elst et al., 2016). Globally, Iran ranks 65th and Poland 32th for the index. This can affect IS climate and compliance. The implementation of the General Data Protection Regulation by European Union member nations is of great importance for IS in Poland (Jackowski, 2018). Mehraeen et al. (2014) stated that although IS in Iranian hospitals is satisfactory, it is nevertheless not optimal and remains an area for development. However, Sołtysik-Piorunkiewicz (2014) reported that IS in Polish hospitals is optimal. This difference affects the relation between IS compliance and participation among nurses in both Poland and Iran (Human Development Report 2019 Team, 2019). For Iranian nurses, only improving the perception of IS importance could improve IS motivation (β = .22, t = 2.38), and through it, IS participation. However, for Polish nurses, the perception of IS importance did not have a statistically significant effect on IS motivation (β = .18, t = 1.08), and it affected IS participation (β = .24, t = 2.96) and IS compliance directly. This result shows that although in both countries only the component of IS importance has a positive effect on IS participation, the mechanism of this relationship is different in these two countries. Iranian nurses who perceived that IS is important were motivated to use it in practice. Polish nurses who perceived that IS is important could get to IS Compliance and Participation.
IMPLICATIONS FOR PRACTICE
Human resource managers in healthcare organizations must focus on the importance of IS in practice by developing procedures and standards and by informing nurses of existing IS rules. Health managers in Iran can use this result and focus on IS importance and motivation to improve IS participation, while health managers in Poland can focus on IS importance and compliance to improve IS participation.
STRENGTHS AND LIMITATIONS
Research on IS among healthcare professionals is new and its importance will continue to increase. The analyses in this study were based on representative data from different cultures. Such studies are rare in the area of nursing (Wagg et al., 2018). We also used new, high-quality psychological tools (Madera et al., 2016). However, this study was limited to only two countries. Therefore, the results cannot be extrapolated to all cultures. Also, many organizational and psychological variables were not taken into account. The study has practical potential – the protection of sensitive personal data will increase with the development of telemedicine (Querstret et al., 2020). Additionally, measurement of IS in nursing is problematic, and the current study has used only a subjective assessment method, without controlling for objective factors such as supervisors’ opinions or reports of IS incidents.
CONCLUSIONS
By setting IS standards and policies, hospital managers can develop IS practices that increase IS participation. Also, holding meetings on the necessity of implementing IS in hospitals can motivate nurses to practise IS. The adapted tool will allow for the assessment of information security in medical care and thus improve the quality of care for patients.
Managers of Iranian hospitals should focus on nurses’ motivation to increase their IS participation, while managers of Polish hospitals should focus on improving IS compliance through appropriate strategies and policies.
Finally, it seems that in both countries, by linking IS policies with human resource management activities such as performance appraisals and training, nurses’ perception of IS importance can be increased, which would facilitate IS participation.